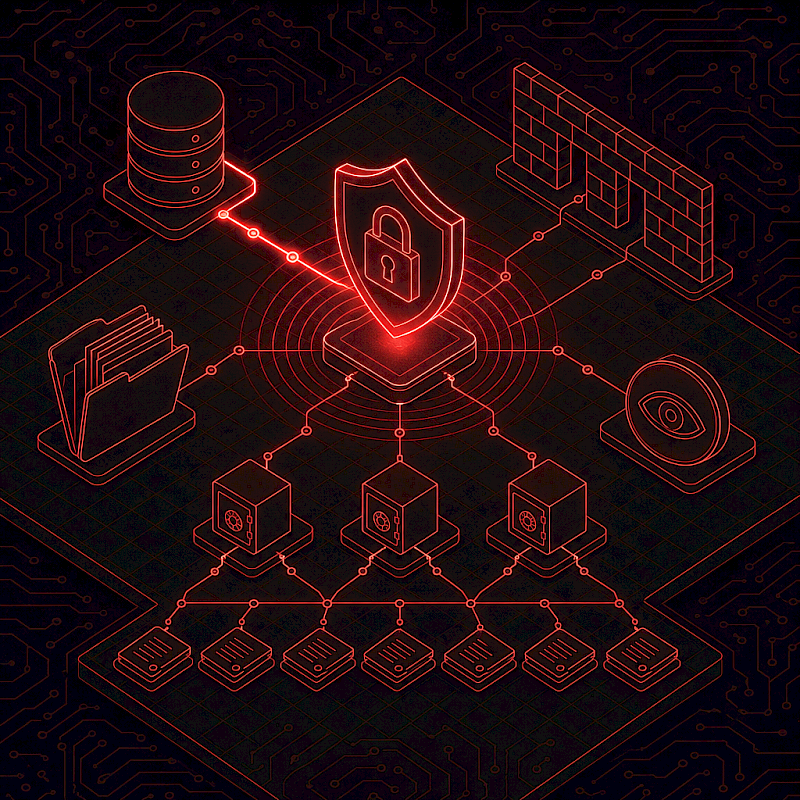
Privacy compliance does not begin with a policy binder. It begins with visibility. If you cannot clearly answer where sensitive data lives, how it moves, who can access it, and which vendors touch it, you will struggle to meet the practical expectations behind both the EU General Data Protection Regulation (GDPR) and the U.S. Health Insurance Portability and Accountability Act (HIPAA).
GDPR is built around accountability - being able to demonstrate that you understand and control your processing of personal data. The HIPAA Security Rule similarly expects an accurate and thorough assessment of risks to electronic protected health information (ePHI), and that assessment is difficult to defend without a credible map of systems, data flows, and access pathways.
Build visibility without boiling the ocean
At Rudolph Technology & Associates, we combine hands-on network engineering and cybersecurity guidance with practical IT leadership - project management, vendor management, and virtual CIO support. In a privacy and data protection context, that blend matters: compliance is ultimately implemented through systems, configurations, and day-to-day operations, not just legal language.
A workable starting point covers four areas:
- System and boundary discovery. Identify the applications, endpoints, servers, and network segments that store or transmit sensitive data.
- Data-path review. Validate how data moves across LAN and WAN, wireless, VPN connections, and cloud services - including remote access patterns.
- Access-path review. Confirm how identities authenticate (admin accounts, shared credentials, remote vendor access) and where access should be tightened.
- Vendor touchpoints. Document which third parties have access, what they access, and where contractual and technical controls need to be strengthened.
Privacy-by-design in the network
The fastest way to reduce privacy risk, and to support GDPR and HIPAA compliance, is to build privacy into the way the network and systems operate every day. Under GDPR, the security principle is summarized as protecting confidentiality, integrity, and availability while embedding privacy by design and by default. Under HIPAA, covered entities and business associates are expected to safeguard PHI and limit use and disclosure to what is permitted - commonly operationalized through role-based access and the "minimum necessary" standard.
The infrastructure controls that deliver the biggest compliance lift are also the ones that reduce day-to-day breach risk:
- Network segmentation that separates clinical, HR, and finance systems from general user traffic.
- Firewall policy rationalization that removes broad "any/any" rules and tightens access by role, device, and location.
- Secure remote access for staff and vendors, with clear rules for who can connect and what they can reach.
- Wireless controls with strong authentication, isolated guest access, and no "shadow" access points.
- Centralized logging foundations so critical systems generate the records needed to investigate suspicious activity.
- Practical identity hygiene - fewer shared accounts, tighter administrator access, and stronger authentication where the environment supports it.
Vendors are a compliance multiplier
Most privacy failures are not caused by a single bad tool. They are caused by too many tools, unclear ownership, and third-party access that grows over time. Under GDPR, vendors that process personal data on your behalf are typically "processors" and require appropriate contracts and safeguards. Under HIPAA, many vendors become "business associates" when they create, receive, maintain, or transmit PHI - which triggers the need for Business Associate Agreements (BAAs).
Common red flags worth fixing first:
- Vendors connecting with shared admin accounts. Move to named accounts with tracked approvals.
- "Temporary" access that lasts forever. Put an expiration date on vendor access and review monthly.
- Unclear retention and deletion. Document where data is stored and how it is removed when a contract ends.
- No defined incident notification path. Establish who contacts whom, in what timeframe, and what information must be shared.
Incident readiness without panic
Even strong programs face incidents - phishing, lost devices, misconfigurations, ransomware, or vendor exposures. Both GDPR and HIPAA expect organizations to assess what happened, understand what data was involved, contain the incident, and communicate appropriately. The operational requirement is the same: fast, accurate fact-finding backed by strong technical evidence. That means logging that answers the right questions, the ability to isolate systems quickly, and a simple playbook that has been rehearsed before it is needed.
Translating technical truth into compliance evidence
When the environment is documented in a way that reflects reality, you can translate technical facts into compliance evidence. For GDPR, that supports records of processing, security measures, and the ability to respond to data subject requests. For HIPAA, it underpins the required risk analysis and helps demonstrate that safeguards are reasonable and appropriate for the environment.
This article is informational and not legal advice. For formal GDPR or HIPAA legal interpretations, consult qualified counsel. If you would like a second set of eyes on your current data flows and access controls, our team can partner with your legal and compliance contacts to put the technical and operational pieces in place. Reach out through our contact page to start the conversation.